Aardvark is a recently introduced vulnerability-discovery agent developed by OpenAI and released in 2024. It is currently available at no cost, making it an attractive option for teams that want to enhance their application-security posture without onboarding expensive enterprise tools. As part of OpenAI’s broader ecosystem of code-analysis and automation technologies, Aardvark focuses specifically on automated vulnerability detection and safe patch generation.
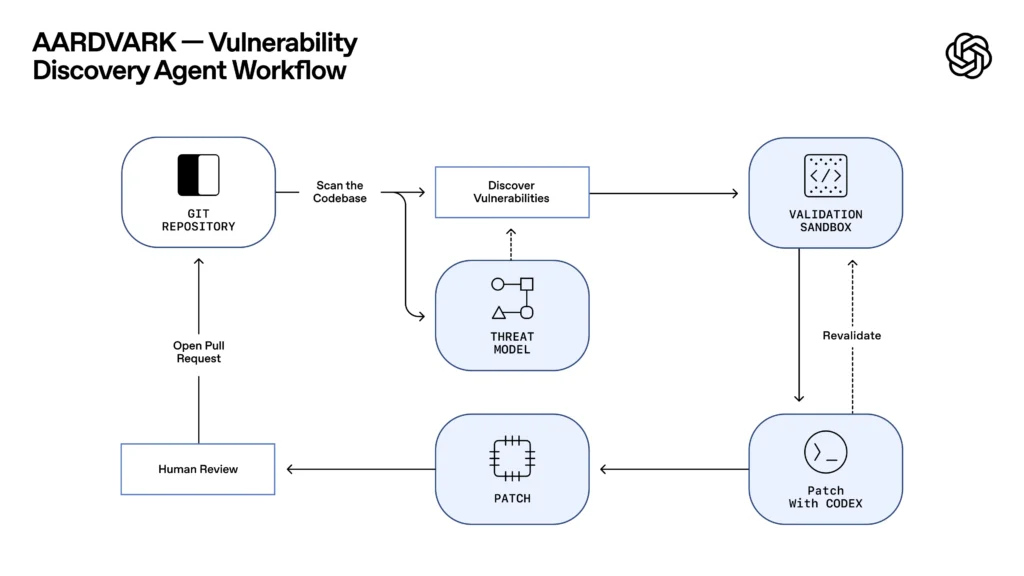
The workflow diagram illustrates a clean, self-contained pipeline: Aardvark begins by scanning an existing Git repository and feeding the codebase into its vulnerability-discovery engine. This engine uses a built-in threat model—represented in the diagram by abstract system symbols—to classify risks and identify flawed patterns.
Findings then move into a validation sandbox, where Aardvark tests exploitability and potential patch effects in isolation. If a fix is required, the system generates a patch using a specialized code-generation module and sends it back through the sandbox for revalidation. Once the patch passes, Aardvark opens an automated pull request, leaving the final decision to human reviewers.
Aardvark fits well into industries facing strict compliance and cybersecurity requirements. Automotive manufacturers can integrate it into software pipelines aligned with ISO 21434 to ensure ECU and connected-vehicle systems remain secure. Public-sector IT modernisation projects—especially those transitioning from legacy architectures—can automate vulnerability detection without expanding internal security teams. Fintech and InsurTech companies operating under BaFin guidance can use Aardvark to maintain continuous scanning across microservices and internal tools, improving audit readiness and incident-response speed.
Integrating Aardvark into an existing buildchain is straightforward. Teams simply add it to their CI/CD configuration, allow it appropriate repository permissions, and enable automated scanning on pushes or pull requests. Aardvark then performs its analysis, creates remediation patches, and submits pull requests for review. This keeps the security workflow tightly coupled with development, ensuring vulnerabilities are surfaced and addressed early—without slowing down release cycles.
Sample integration to GitLab
Aardvark operates in three main stages:
- Scan: The agent scans the repository for potential vulnerabilities and produces a detailed report.
- Validate: Findings are tested in an isolated sandbox to ensure reliability and minimize false positives.
- Patch: Aardvark generates code fixes and pushes them to a feature branch. Optionally, it can create a merge request automatically for team review.
Example CI/CD Configuration (.gitlab-ci.yml)
stages:
- scan
- validate
- patch
aardvark_scan:
stage: scan
image: python:3.11
script:
- pip install aardvark-cli
- aardvark scan --repo . --out aardvark_report.json
artifacts:
paths:
- aardvark_report.json
aardvark_validate:
stage: validate
image: python:3.11
script:
- aardvark validate aardvark_report.json --sandbox
needs:
- aardvark_scan
aardvark_patch:
stage: patch
image: python:3.11
script:
- aardvark patch aardvark_report.json --apply
- git config --global user.email "aardvark-bot@example.com"
- git config --global user.name "Aardvark Bot"
- git checkout -b fix/aardvark-$CI_PIPELINE_ID
- git add .
- git commit -m "Aardvark automated patch"
- git push origin fix/aardvark-$CI_PIPELINE_ID
needs:
- aardvark_validate